In the early stages of scientific management, quality control sounded too ambitious; yet the concept was later heightened by the introduction of ZQD or “zero-defects.” This sounded incredulous at first, until the companies underwent process improvements and learned about the “poka-yoke” technique.
The Viability of Attaining Zero Defects
Aiming to achieve “zero-defect” may seem too idealistic as a process improvement goal, but one has to perceive that the concept is being taken in its context as a form of quality management technique.
Under the Six Sigma strategy, this requires rigorous research and statistical analysis for the sole purpose of locating and eliminating errors. Any error detected could stem from less than 3.4 defects for every million opportunities presented. Thus the discipline continues by applying the “poka-yoke” or error-proofing technique, in anticipation of any mishaps.
This technique was developed by Dr. Shigeo Shingo, a Matsushita Industrial Engineer, as he recognized the possibilities of human errors. Slip-ups may originate from both the workers involved with the manufacture of a product or could be instigated by the end-users or the consumers.
Principles Observed:

Proofing a product design for errors is about establishing the common mistakes made in relation to the product’s manufacture or use. The action taken is to incorporate fail-safe mechanisms to prevent the error from occurring.
However, it is possible that adding a built-in prevention device would make the product too expensive and would be regarded as not economically feasible. If this is the case, the alternate route taken is to incorporate the fail-safe mechanism by way of design.
There are five principles observed in applying error-proofing techniques:
Prevention – in which the objective is to eliminate any possibilities of a mistake being commited.
Replacement – this involves redesigning or substitution of a component in the product’s design to make error-prevention more reliable.
Facilitation – this denotes the process of simplifying the system to avoid complications from which defects due to variables may stem.
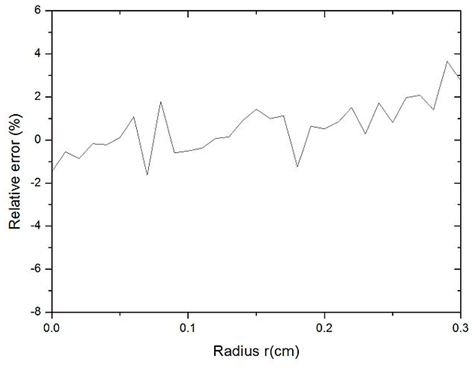
Detection – which means rigorous research and testing procedures applied in order to detect variances and deviations.
Mitigation – incorporating a component that would minimize if not eliminate the detriments in the event that a possible error does take place.
Procedural Steps:
1. Identify the Defect and Track the Effect –This is done by performing some of the most common root cause analysis methods and problem-solving techniques, e.g.:
Data Gathering – Problems or defects should always be factual, and the related data are usually derived by observing the actual processes. If the product is still in its design stage, data related to the processes are created and tested. However, any information gathered is useful only if it is presented by way of charts, maps and graphical displays that will depict the events leading to the identification of the root cause.
Statistical Analyses –These are used in conjunction with the data displays as a means to extract correlation between factors, progression and regression of the events and the variables (multivariates) produced by the main causal factor or the root cause.
Using Simulations – The simulations are created by using computer modeling software. Experimentations of the actual process under study are conducted for purposes of exploring all probabilities. The aim is to collect all data that lead to the root cause of the known or anticipated problems.
Analyses of Past Failures and Their Established Root Causes – The process involves the review of the physical evidence and subjecting it to further testing by using special tools or by gathering additional data from actual interviews. One of the testing methods used is “accelerated testing.” The approach aims to obtain information regarding the results of a more severe test environment. However, caution should be taken when extracting information from this type of test by avoiding failure modes that are not common to the normal use of the design or product. Factors often used for testing either the life cycle or the stress threshold include high humidity, high levels of vibrations, extreme temperatures or higher rates of power frequencies.
Use The 5-Whys Method – A root cause analysis method performed by asking five or more “why” questions about a given event. The answer elicited would prompt another why question that delves deeper into the underlying conditions for purposes of unraveling the real cause.
Analyze by Using “What is and What Isn’t” Method – This entails sorting the problem into what it is and what it is not, what happened or what didn’t happen, when did it happen or when it doesn’t happen, what changes took place or what didn’t change and other similar questions related to the circumstances of the event.

2. Review the existing standard operating procedures (SOP) in observation, during the specific period related to the creation of the defect.
The aim is to review the organizational routines and to isolate those that have a direct effect in the creation of the product and its defective quality. SOPs may not be the possible root causes but they provide critical information that would lead to the causal factors and, eventually, the root cause.
By unraveling and studying the routine exercises performed, theories from various branches of social and behavioral sciences can provide the explanations why certain variables or variances occur. However, this method should be applied by establishing a model of procedural or operational routines. The approach to its analysis is by:
-
Examining only one related aspect and not the entire divergence of purpose for which the procedure was developed.
-
Considering the relationship of the aspect under study to the other purposes, and then determine if those relationships had any influence over the defect.
3. Ascertain if certain deviations or variables emanate from the performance of a routine function and investigate the cause of the deviation.
The most common method of analyzing the root cause of a variable is through the “fishbone analysis ” method. Take note of individual factors like skills, knowledge of the procedures, habits, decorum, known medical history, and other similar factors that phenomenally contribute to the creation of a deviation. Establish a pattern that is easily recognizable in a routine system of activities.
4. Identify the point at which the deviation is formed or created. Make a checklist of the specific conditions or circumstances that spawn the creation of the variable.
Examples of these conditions include but are not limited to:
- Procedural adjustment.
- Change or replacement of tools or equipment employed.
- Increase or decrease in dimensions.
- Infraction against specification or policy.
- The existence of multiple parts or mixed classes of ingredients or components.
- Other factors related to the specific point where they converge during the creation; e.g., rate of repetition or frequency; intensities, symmetry or characteristics of physical conditions.
5. Develop and implement the applicable error-proofing device based on the following requirements:
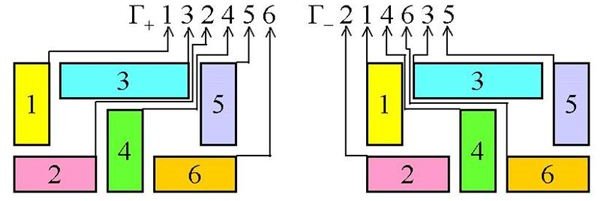
Physical Contact – Lack of physical contact between specific components triggers the chain of events; hence the error-proofing device to be developed is one that will abort all other procedural functions, if the product senses the absence of contact.
Sequence of Count – The system operates according to a fixed number of procedures or a definite number of parts, as a requirement. The failsafe mechanism to be incorporated is one that will alert the worker or the user if the total number of sequences required has not been met. The machine used or the product will be prevented from continuing with the other procedures.
Sequence of Motion – The system recognizes a sequence of activities, or each activity is dependent on a specific action before the next step goes into motion. The device will produce a warning signal that requires the performance of an action before it can proceed to the completion of a procedure.
Examples of Error-Proofing Mechanisms to Consider:
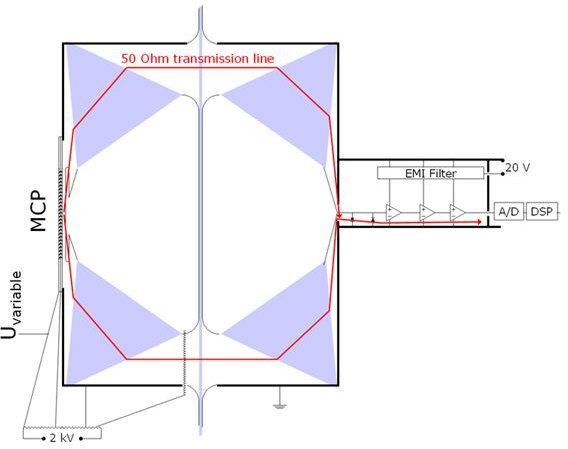
(a) Limiting Switches – These are typically electromechanical devices used to detect the presence or absence of physical contact.
(b) Proximity Detectors – The detector emits a high-frequency magnetic field when an unrecognized element enters the scenario.
(c) Laser Displacement Detector – A laser beam is in place to detect the requirement by reflecting on a programmed target. If the target is recognized and meets all conditions, the procedure continues on to the next stage.
(d) Visual Sensor – Typically aided with the use of a camera that provides a situational view to be compared against a standard view stored in a computer. Inconsistencies or dissimilarities detected by the program will cause the computer to reboot or shut-down.
(e) Counting or Timing Devices – Counters recognize a sequence of events and are programmed to shut down the system if a set number of events or activities is not completed.
(f) Photoelectric Sensors – The sensor is made up of three components:
- The through-beam, which is the source of the reflective light;
- The reflective unit or the receiver of the beam, which requires that the light-received will bounce-off to another unit;
- The bounce-back unit, which senses if the beam reflected is broken.
(g) Ultrasonic Detectors – This mechanism emits high-frequency radio waves and will look for a deflection or bouncing-back motion of the radio waves it emitted.
As a recapitulation of the principles and procedures observed in applying the “poka-yoke” technique, we can easily glean that thorough research and analyses are performed before the error- proofing method is adopted as the solution. It is important that the solution has to be decidedly simple in order to avoid creating complexities and false signals. In addition, the main focus of the product is still the practical and economical value it presents to the customer.
Ideally, therefore, process improvement that is enhanced by incorporating fail-safe designs should be the primary goal of a production system.
Reference Section and Image Credits:
References:
- Design Process Error-Proofing:Strategies for Reducing Quality Loss in Product Development — https://webcache.googleusercontent.com/search?q=cache:pnergBqq0ogJ:mml.stanford.edu/publications/2005/IMECE2005-79453.pdf+need+for+mistake+proofing+devices&hl=en&gl=ph
- Zero Defects -What is it? —https://www.managers-net.com/zerodefects.html
Image Credit Section:
- By BoH / Wikimedia Commons
- By TT-97976 / Wikimedia Commons
- By Zacabeb / Wikimedia Commons
- By Lucas753 / Wikimedia Commons
- Released by the United States Navy with the ID 060417-N-0490C-002
.As a work
of the U.S. federal government, the image is in the public domain.



